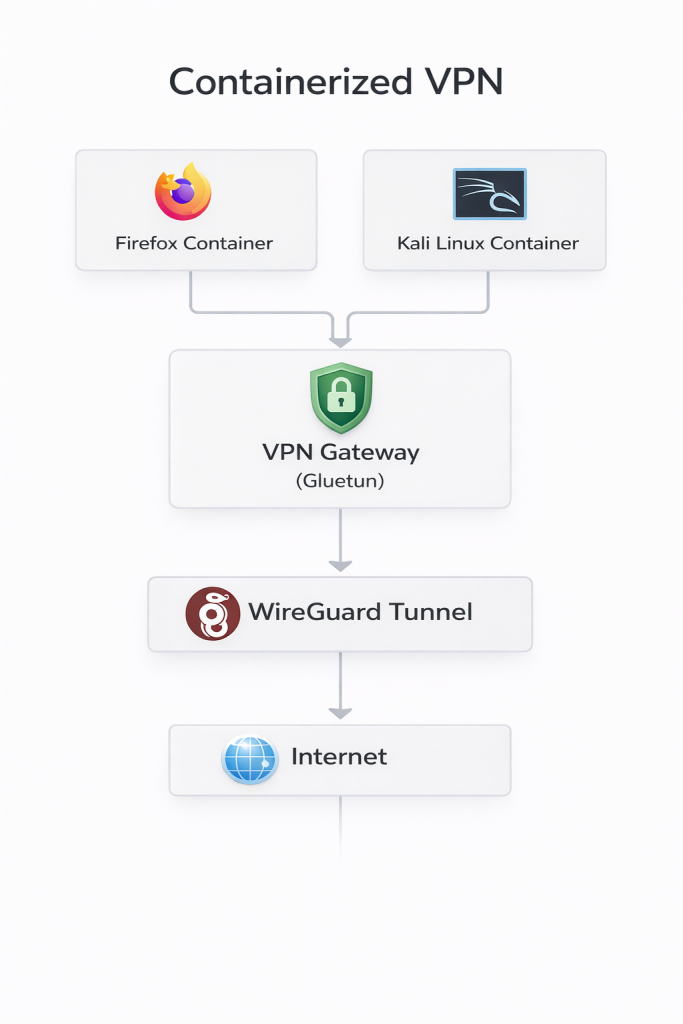
Containerized VPN Gateway
This project isolates workloads inside containers and routes all of their network traffic through a dedicated VPN gateway.
Instead of installing VPN clients directly on the host, containers such as Firefox and Kali Linux share the network stack of a Gluetun VPN gateway container running which establishes a WireGuard VPN tunnel. DNS requests are also encrypted at the router level using DNS-over-TLS (DoT).
This design ensures these containers can’t access the internet outside the VPN gateway.
Architecture
The network path is intentionally simple:
Container → VPN Gateway
→ WireGuard → Internet
Implementation
The environment runs using Docker and docker-compose.
Key components:
– The Gluetun container establishes the VPN tunnel, DNS encryption and firewall rules
– DoT encrypts DNS resolution through unbound
– Enables the Firefox container and Kali Linux containers browsing and operating from a different region
The containers attach directly to the gateway container’s network namespace so traffic stays within the VPN.
Operations
The gateway container acts as the enforcement point for outbound connectivity.
If the WireGuard tunnel drops, Gluetun blocks outbound traffic, preventing containers from reaching the internet outside the VPN. Containers can be added, removed and rebuilt quickly without affecting the host system or amount of devices registered over the VPN.